

Everywhere, except India, it’s about 3%.
With India the average is a bit more than 4%.
Errar es humano. Propagar errores automáticamente es #devops


Everywhere, except India, it’s about 3%.
With India the average is a bit more than 4%.


Wait.
Does Portainer ask your email? I haven’t used it in years. I though it was just a container that you run, with mounted docker socket, and that’s it.
Is it now doing some “telemetry” and sending user data, like email, to their servers? If so, I’m glad I’m not using that anymore.


Well, thank you for pointing me to this project. Didn’t know about it. I’ve just built it. So, the part of I’ll do my best to see what can I help with applies here to.
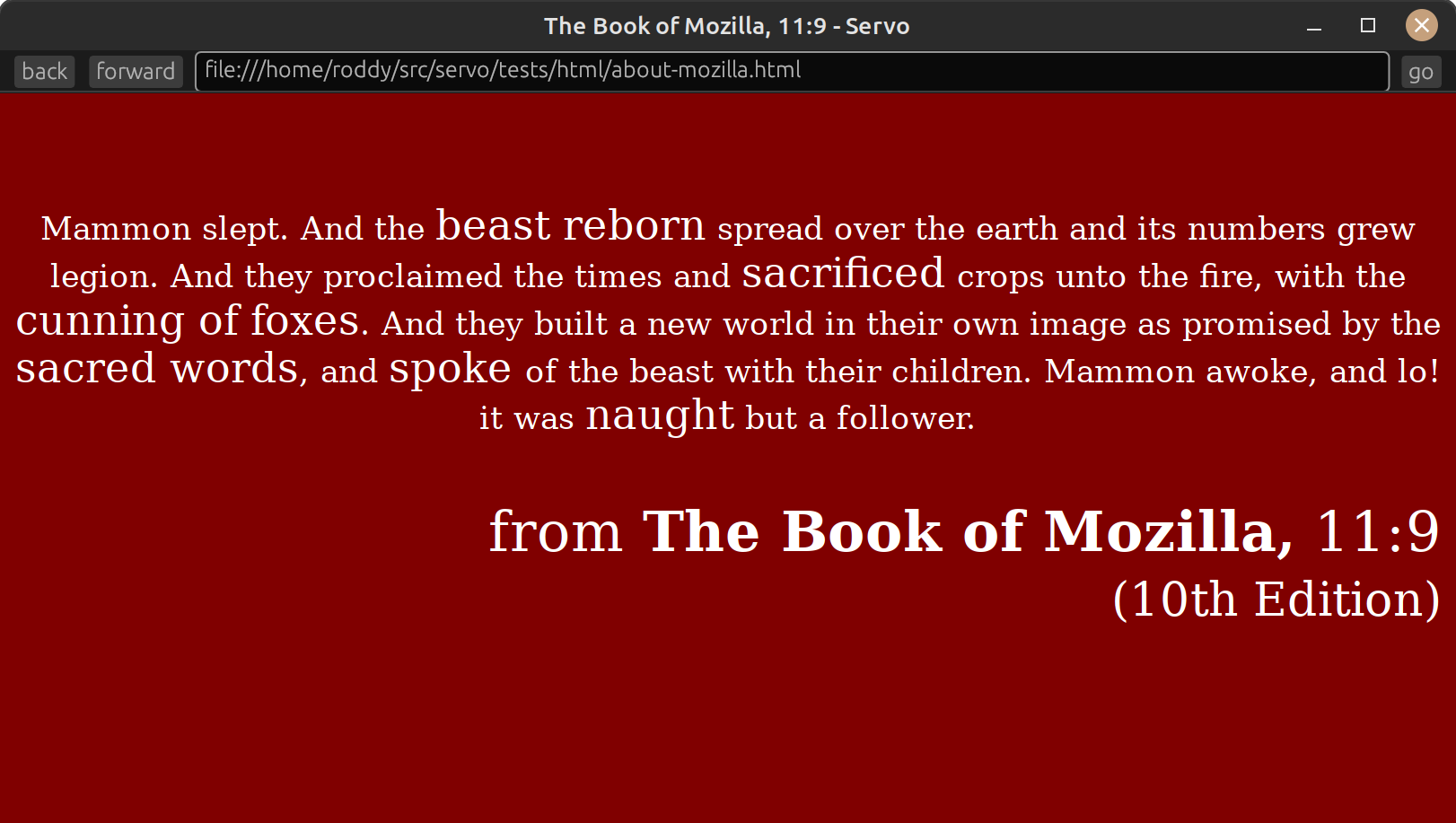


The project management may have some obvious problems (jOin dIsc0Rd sErVEr; w0rD “thEy” t0o p0liTicAl). But we really need an alternative to browsers funded by Google (Chrome and Firefox).
So I’ll do my best to actually build from sources and see what can I help with. Attacking the author is helping nobody.
And for the folks who are saying “wHy n0t rUst”, you can always show me the (rust) code.


VPS + VPN is the cheapest option I believe for the services. It doesn’t have to be “elaborated”.
You can port-forward public VPS ports to your private addresses/ports. If you don’t want to use iptables you can use firewalld.
The only “but” will be latency. For gaming it won’t perform as you may need.
It’s no longer open source. Big Deal in my books.
Vault features are cool. I really like it. But with Hashicorp now there is this big risk of “rug pulling” regarding its license.
The wise thing, in my opinion, is to avoid this company as much as possible.


If your comments have been federated to other instances, they will be there until they are deleted locally. If someone clicks on your user profile, they will get a DNS error if the domain is no longer there. Images in the comments pointing to you instance will be broken too. Nothing terrible actually happens.
Migrating accounts a la Mastodon is not happening soon in Lemmy.
My advice is: Go on and save some money.


Sorry to read that.
I’ve dded an external drive instead of an SD card once by mistake. I’ve never felt more stupid than that day.
It’s running NetBSD, isn’t it?


Some security tips:
Firewall should block everything by default, and you start allowing incoming and outgoing connections when you need them or if something fails.
Disable passwords and root access in ssh daemon.
Use fail2ban or something similar to block bots failing to log-in.
Use random long passwords for everything (eg: like databases). And put then in a password manager. If you can remember the database password, it’s not strong enough. If you can remember the admin password for a public web service, it’s weak.
Don’t repeat the passwords. Everything should have its own random long password.
.env files and files with secrets should be readable only by its service user. Chmod them to 400.
Monitor logs from time to time to see if something funny is happening.


Random ports are easy to discover and there are tools to discover what service is behind a port.
It’s annoying for the legitimate user and easy to bypass by an actual attacker.
Also, if you use a random port above 1024 it could be a security issue since any user could star listening if the legitimate process crashes.
See this


Nothing illegal is being discussed.
But I’m happy to talk about Jolly Roger.
Wow! this is exactly what I needed. Although, I didn’t exactly ask for it.
Thank you very much
Thanks to both of you.
I had the hope that DMARC, SPF and DKIM was stuff I could just ignore if not sending email. It seems I was wrong about that.


see federated network
looks inside
mastodon.social
I’ve got 3 tricks for ya:


Pros:
Cons:
Welcome to Lemmy. Hope you enjoy it.
You may have one psql server per region and then use Bucardo to synchronize them.
I’ve never done this in production, so take my advice with a grain of salt.
git is already a decentralized version control software. Your local git repos are mirrors by themselves.
Put some
git fetchin a server crontab, and you’re done. You can access them via ssh if your user have permissions.